
Tag DevOps


Unpacking Our Findings From Assessing Numerous Infrastructures – Part 2
Read MoreUnpacking Our Findings From Assessing Numerous Infrastructures – Part 2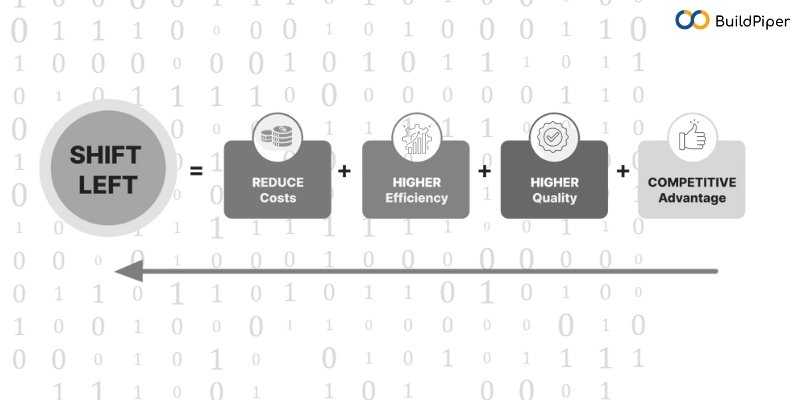
How to Adopt Shift Left Security on the Cloud?
Read MoreHow to Adopt Shift Left Security on the Cloud?
My learning in Migration of MySQL from 5.7 to 8.0
Read MoreMy learning in Migration of MySQL from 5.7 to 8.0