

Ideas That Drive Innovation

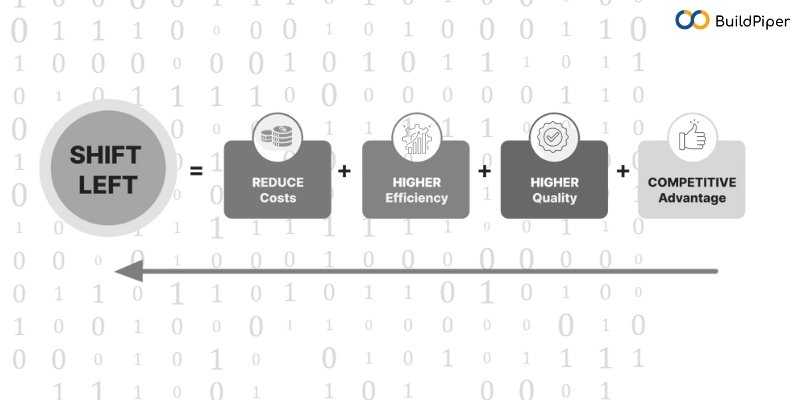
How to Adopt Shift Left Security on the Cloud?
Read MoreHow to Adopt Shift Left Security on the Cloud?
My learning in Migration of MySQL from 5.7 to 8.0
Read MoreMy learning in Migration of MySQL from 5.7 to 8.0
Demystifying Oracle Cloud Infrastructure (OCI): A Comprehensive Introduction and Architecture Overview
Read MoreDemystifying Oracle Cloud Infrastructure (OCI): A Comprehensive Introduction and Architecture Overview
Exploring the Power of IAM Roles Anywhere for Secure Access Management
Read MoreExploring the Power of IAM Roles Anywhere for Secure Access Management
How Can IT Services Adapt and Benefit From Platform Engineering?
Read MoreHow Can IT Services Adapt and Benefit From Platform Engineering?
Unpacking Our Findings From Assessing Numerous Infrastructures – Part 1
Read MoreUnpacking Our Findings From Assessing Numerous Infrastructures – Part 1
Apache Cassandra Migration Last Episode: 3x to 4x Migration
Read MoreApache Cassandra Migration Last Episode: 3x to 4x Migration
Applications Hosting on ECS
Read MoreApplications Hosting on ECS
OpenSearch Alert Integration with SNS
Read MoreOpenSearch Alert Integration with SNS
GCP to Azure VPN Tunneling with Multiple Networks
Read MoreGCP to Azure VPN Tunneling with Multiple Networks